Recently in the world of blockchain, besides an endless stream of tears, the most concern is security. In the current digital currency market, more than 90% of smart contracts use the ERC20 standard. There is no doubt that the ERC20 standard has become the norm for all exchanges, wallets, and project parties. ArmorsLabs’ Intelligent Contract Scanning System (IDS) analyzed more than 10,000 ERC20 smart contracts on Ethereum and found that there are huge security holes in the approach of the ERC20 standard’s approach, resulting in the risk of vector attacks on tokens. So based on the market statistics, Armors team pointed out that there are at least more than 60% of the digital currencies were used this vulnerability in smart contracts.
Since October 2017, Armors team has been committed to the ecological construction of smart contracts and vulnerability analysis. Here we give you the “jaeden” vulnerability recently named by ArmorsLabs. The loophole is by far the most comprehensive loophole in ERC20.
Let us analyze the following loopholes for everyone:
The standard interface mentioned by ERC20:
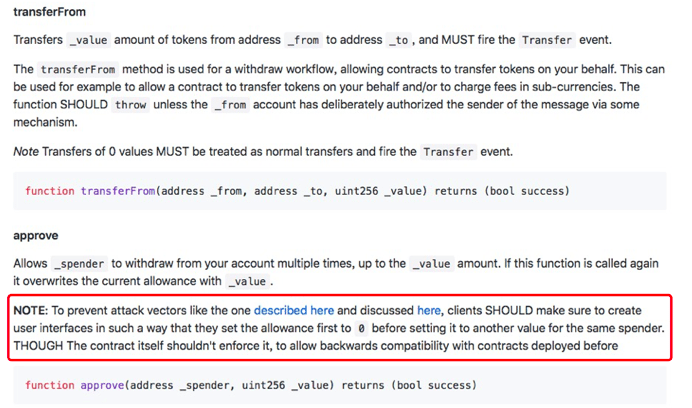
The original spirit of the designing of Approve and transfer form aims to serve Decentralized Exchange. Users can authorize a third party to manage a certain amount of token.
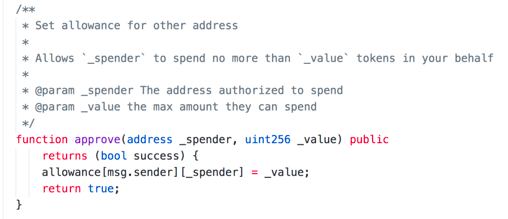
In the Ethereum official ERC20 Demo, there is a vector attack vulnerability in the code of the approve function. Under the simple description, Party A authorizes Party B to manage its own digital currency. If Party A wants to change Party B’s authority, Party B can transfer away the authorized currency in advance, and then can also charge the newly authorized currency again, resulting in Party A’s repeated Transfers, resulting in the loss of digital property.
This type of authorization is widely used in decentralized exchanges, third-party payments, and quantitative fund management.
In the digital currency world, smart contracts are laws – Code is Law! Unless there are actual equivalents, offline transaction contracts or legal constraints. When code goes bust that means the law goes bust! The risks put up by transfer chicanery cannot be turned around! This kind of loophole authorization mechanism will bring a security crisis to digital assets worth billions or even billions of dollars.
This vulnerability, which is a major security risk caused by Ethereum standards, has been named “jaeden” by Armors and has been submitted to the cve platform. In addition to this vulnerability, Armors vulnerability analysts also discovered that there are more loopholes in the currency, such as:
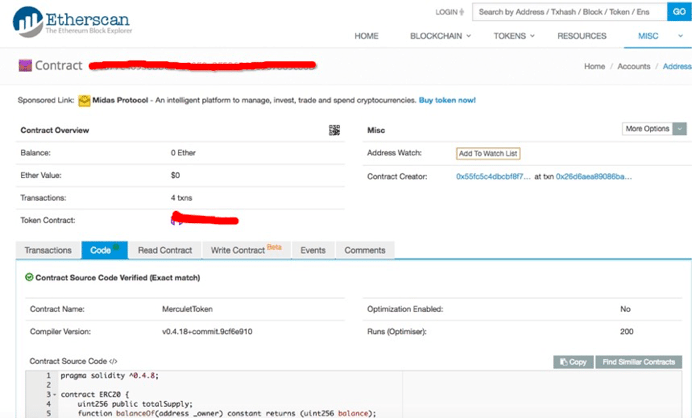
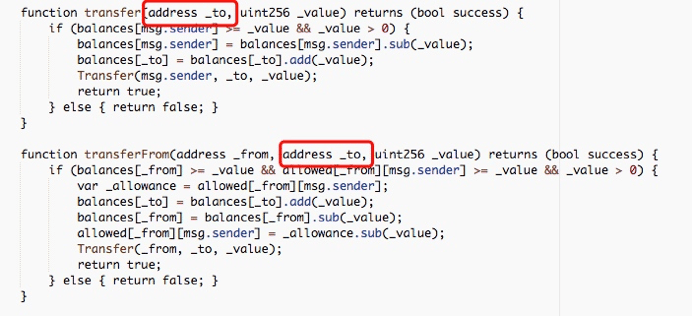
This contract has not blocked nowhere-transfer which means that this token economic system can easily be thrown into disorder if some aggressive banker put massive token into this nowhere aiming at share-controlling.
ArmorsLabs is responsible for each digital currency investor and recommends that each exchange and project party introduce more and more experienced audit partners and re-review their smart contract codes. Once you find a problem, seek solutions as early as possible to avoid irreparable damage.
About ArmorsLabs
ArmorsLabs, as the world’s top blockchain security laboratory, extends from the full ecosystem platform for smart contracts to overall blockchain security. Armors provides a complete blockchain immune system that uses unsupervised machine learning and AI algorithms to build multidimensional models for DApp. The team members are from world-class Internet companies such as Apple, Google, 360, Baidu, and Tencent, and graduated from Berkeley, Carnegie Mellon, and Tsinghua universities. Currently, Armors has in-depth cooperation with EON, SOC, XMX, DACC, CWV, HyperPay and other projects. In the future, Armors will work hard to build a set of general-purpose smart contract security specifications and work hard to build a blockchain security ecosystem.
More information is welcome to visit: http://www.armors.io























